OT cybersecurity has become a major challenge for industry. However, in many industrial companies, efforts to efforts are still largely focused on IT systems systems (networks, servers, user workstations).
But what about industrial equipment, PLCs, sensors and production lines? That’s precisely where most of the risk lies today!
What is OT cybersecurity?
Operational Technology (OT) cybersecurity refers to all the practices practices, technologies and measures designed to industrial systems against cyber threats.
Unlike IT cybersecurity, which focuses on information systems (servers, networks, workstations), OT cybersecurity directly concerns physical equipment and industrial processes. equipment and industrial processes.
In particular, it aims to guarantee :
- the continuity of operations
- integrity of production processes
- safety installations and people
In industrial environments, a cyber attack is more than just a data leak or computer downtime. It can have direct consequences on production, quality and even the physical infrastructure.
That’s what makes OT cybersecurity both specific… and critical.
Understanding the industrial systems (IS) environment
OT environments are based on a specific architecture, designed to control and supervise industrial processes.
There are generallyseveral layers:
- Visit sensors and actuators, which interact directly with the physical world
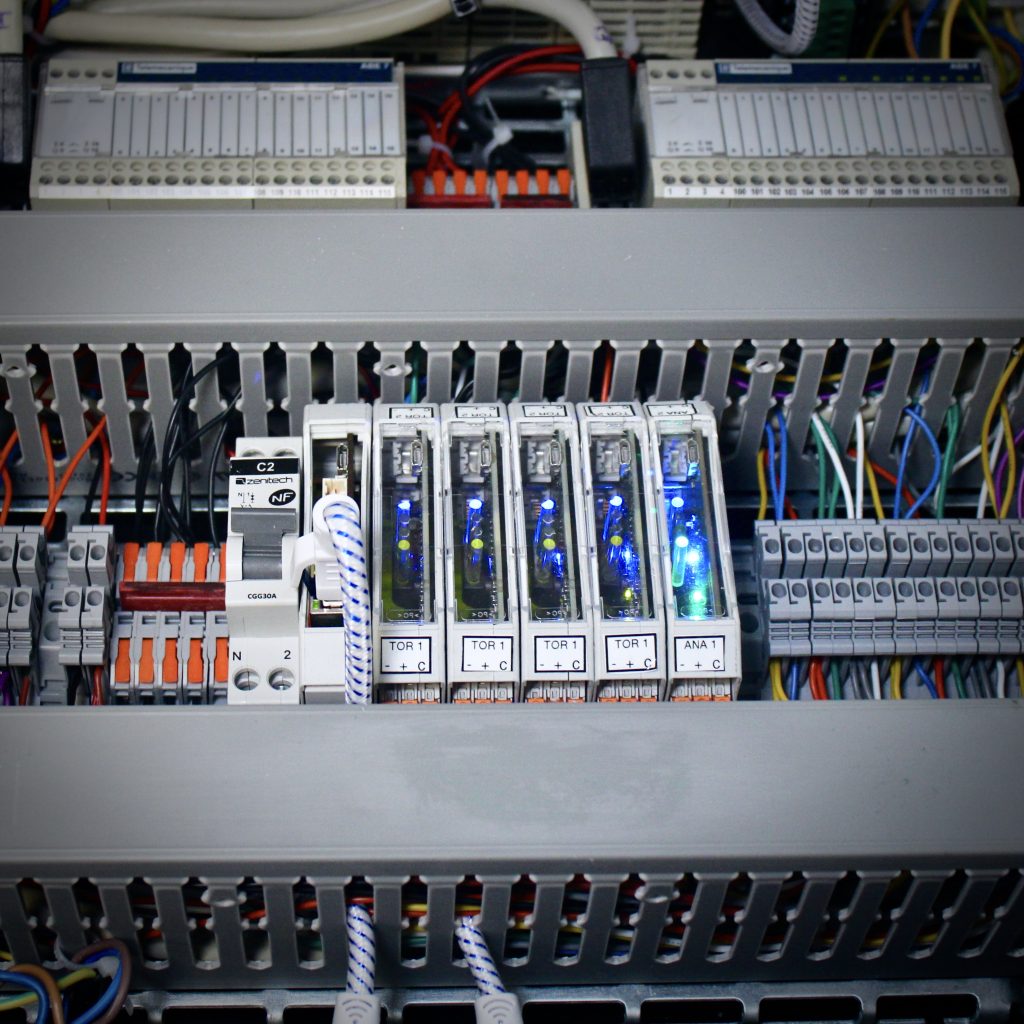
- The industrial controllers (PLC), which execute commands and control equipment
- The supervision systems (SCADA), which centralize data and provide global control
- The ICS (Industrial Control Systems), which encompass all these components

In this architecture, data flows from the field to the supervisory systems, via the PLCs which act as intermediaries. Understanding this organization is essential to grasp the challenges of OT cybersecurity… and its blind spots.
An explosion in cyberattacks targeting industrial environments
Between 2021 and 2023, the average number of industrial attacks reported each month will rise from from 31 to 73, an increase of +53% in just two years (source: CSO Online).
The figures speak for themselves. The cyber attackers no longer target IT systems alone. They are now attacking PLCs PLCs, sensors and sensors and actuators and control and production systems.
Invisible EO cyberattacks with real consequences
In many cases, an OT cyber attack does not block production with an immediate shutdown. It is more insidious and creates a slow drift:
- a modified order,
- a falsified sensor value,
- abnormal but discreet behavior.
As a result, systems continue to as if nothing were wrong, and dashboards display data that looks coherent, but the physical reality is altered.
And that’s what makes IoT cybersecurity so complex. complex.
A structural flaw in the industrial data chain
In classic industrial architectures, PLCs play a central role: they collect, filter and transmit data to supervisory control systems (SCADA) SYSTEMS.
But this creates a major problem, as IT tools and supervision systems only see data that has already been already transformed data. They have no visibility of the equipment’s raw signals.
In fact, if a PLC is compromised, the data reported may be false, alerts may be absent, and operators may only be able to make an incorrect reading of the situation.

A case in point is the attack on Moscollector in Russia, where sensor data was manipulated, giving a false view of the real state of the network.
As the information is biased at source, all subsequent layers become blind.
OT cybersecurity: why prevention is no longer enough
According to CISA, 80% of OT attacks originate in IT. In other words, even with robust IT cybersecurity, a vulnerability will eventually be exploited. there is no such thing as zero risk.
So the question is no longer just: “How do I prevent an OT attack?How to prevent an EO attack? but rather: “How to detect, understand and react quickly to an IoT cyber attack?”
This is where the notion of OT resilience.
Against this backdrop, regulatory regulatory developments reinforce this approach. The European directive NIS2, which is gradually coming into force, requires industrial players to step up their level of cybersecurity, with particular emphasis on system system resilience. In concrete terms, this means setting up capabilities for anomaly detection incident management and disaster recovery plans (DRP).
Towards OT cybersecurity based on physical reality
You need to observe what’s actually happening on the equipment, analyze its signals and check command execution.
The raw electrical signals (input/output) are a key source of information for :
- verify that a command has been executed
- detect inconsistencies
- identify abnormal behavior that is invisible elsewhere
Solutions now exist to capture these signals directly at source. Installed as close as possible to the equipment (e.g. on a DIN rail), they can be used without modifying the existing architecture:
- analyze inputs/outputs in real time
- compare order and execution
- detect anomalies even when PLCs are compromised
This approach provides visibility independent from traditional systems.
OT cybersecurity: the strategic challenge of securing industrial equipment at source.
OT can no longer be considered a blind spot in cybersecurity. It lies at the heart of production, industrial performance and operational risks. Today OT cybersecurity is no longer just a technical issue. It’s a financial, strategic and systemic issue.
Industrial environments are changing fast, and so are the threats they pose. It is necessary to go to the source of data, observe physical reality and detect anomalies where they appear, in the equipment itself.
Only then can manufacturers truly strengthen their resilience in the face of cyber threats.
FAQ - OT cybersecurity
What is OT cybersecurity?
OT (Operational Technology) cybersecurity covers all practices designed to protect industrial systems, such as PLCs, sensors or supervision systems, against cyberattacks. Its aim is to guarantee the continuity of operations, the integrity of processes and the safety of installations.
What's the difference between IT and OT cybersecurity?
IT cybersecurity protects information systems (networks, servers, data), while OT cybersecurity concerns industrial systems and physical equipment. An OT cyber attack can have a direct impact on production, machinery and, in some cases, personal safety.
Why has OT cybersecurity become critical?
Industrial environments are increasingly connected, making them more vulnerable to cyber threats. What’s more, attackers now target industrial equipment directly, sometimes invisibly, but with real consequences for operations.
What are the main OT cybersecurity risks?
Risks include :
- modification of industrial orders
- falsification of sensor data
- equipment stoppage or damage
- impacts on production quality
- risks to plant safety
Why are some OT attacks so difficult to detect?
In conventional industrial architectures, data is filtered by PLCs before being passed on to supervisory systems. If these systems are compromised, they can continue to display consistent information, even if the physical reality is altered.
How can we improve the cybersecurity of industrial systems?
Improving OT cybersecurity involves a number of actions:
- secure IT/OT access and connections
- strengthen industrial network supervision
- test systems regularly
- and, above all, improve visibility close to equipment
Why is field visibility essential in OT cybersecurity?
Good visibility enables you to understand what’s really happening on your equipment. By accessing unfiltered data, it becomes possible to detect anomalies or discrepancies between commands and their execution, even if traditional systems have been compromised.







